CHF
3.00
per mailbox and month
E-Mail Security (Perception Point)
Intercepts any email-based attack within seconds.
Protect your emails from spam, phishing, fraud, malware and other attacks before they reach your Microsoft 365, Google Workspace or Open-Xchange mailbox. Use our advanced Cloud email security solution, powered by Perception Point.
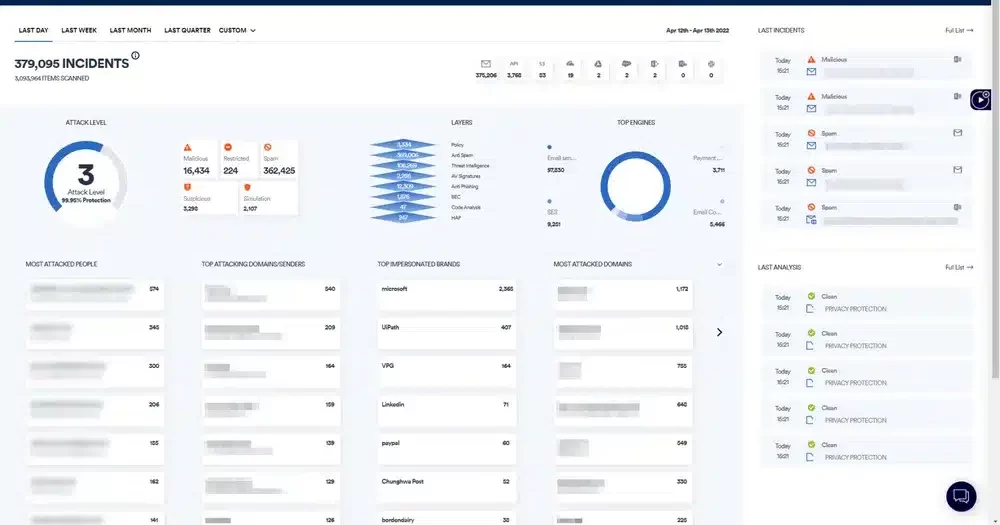
In contrast to conventional sandboxing solutions, every single piece of content (emails, files and URLs) is analyzed to an unlimited extent. A clear assessment is made in a matter of seconds before the content reaches the respective end user.
Block advanced threats that can evade conventional defenses (such as APT and zero-day attacks) with unique CPU-level malware analysis that enables earlier intervention in the attack chain than other technologies.
Detect hidden malicious content by recursively unpacking embedded files and URLs and then analyzing them separately with dynamic and static detection modules.
With this purely Cloud deployment, you can integrate directly into the existing email system without additional configuration to reduce the administrative overhead normally associated with deploying Secure Email Gateways (SEG).
Support your service delivery and security teams with direct access to Cyber and email security experts who analyze all customer traffic for malicious intent and malicious content - with continuous reporting and support.
Benefit from unrivaled detection speed that allows you to stop threats before they reach end users - unlike the reactive approach of traditional email security technologies.
All functions compact in one platform
Configure your protection within an efficient platform.
Minimize email risks with powerful threat intelligence, signature-based malware detection, URL reputation checks, unique image recognition algorithms and machine learning capabilities with DMARC record checks.
Better protection for M365
Strengthen the protection of Microsoft 365 with an additional, fast and comprehensive security solution.
Many users find the built-in protection of Microsoft 365 too slow and insufficient against complex attacks. Our solution ensures that email threats are stopped at lightning speed.

Malware, such as viruses, ransomware and Trojans, often spreads via malicious files and links. Thousands of new variants are added every day. Normal security solutions reach their limits, especially when it comes to sophisticated evasion strategies and the protection of online collaboration platforms.
E-Mail Security protects against such attacks and uses:
- Anti-evasion: Finds hidden malware.
- Threat Intelligence: Always stays one step ahead of new threats.
- Antiphishing Filter: Detects dangerous links.
- Antivirus: Stops known malware.
- Next-Generation Dynamic Engine: Detects attacks that bypass normal security measures, such as zero-day and APT attacks.
Phishing attacks, which are responsible for 91% of all cyberattacks, use sophisticated methods to deceive users in order to obtain sensitive information. They pretend to be trustworthy sources with files, links or texts.
E-Mail Security protects against such attacks and uses:
- Anti-evasion: Detects hidden phishing attempts.
- URL reputation check: Blocks known dangerous links by analyzing them with four leading reputation services.
- Image recognition: Stops unknown dangerous links by analyzing images and logos on websites.
- Threat intelligence: Uses information from six leading sources and Perception Point's own intelligence engine.
Attacks that pretend to be someone else can easily fool employees into thinking they are communicating with a known person. Many of these scams use only text and no malicious files, which makes them particularly difficult to detect.
Protect yourself from such attempts at deception by:
- Antispoofing: Stops attacks without malicious files with advanced algorithms that check email settings such as IP reputation and email authentication.
- Anti-evasion: Scans emails thoroughly to find hidden threats.
- Protection against malicious content: Prevents full-scale scams with threat, phishing and virus detection tools.
Zero-day and APT attacks exploit unknown vulnerabilities in software, often months before they are discovered, making them very difficult to detect. Many common protection methods such as sandboxing (a kind of test environment) or CDR (the removal of malicious parts from files) are not sufficient because attackers can bypass them.
Use advanced technology that can detect such attacks at an early stage. It performs dynamic scans that work at the processor level and can detect and stop dangerous code before it causes damage.
Email attacks are difficult to detect these days because attackers use sophisticated methods to circumvent conventional security measures. They hide malicious content in ordinary files or use complicated links that only become active when the recipient opens them - normal security solutions have a hard time dealing with this.
In response, the e-mail security solution relies on a special technology that goes far beyond what conventional methods can do:
- Anti-evasion: This technology breaks down emails into their smallest components and checks them quickly and efficiently for hidden dangers - in less than 30 seconds, whereas older systems often take over 20 minutes.
Attempts to take over accounts are very popular with cyber criminals. They target companies' email and bank accounts. Such takeovers happen when hackers gain access to a legitimate account and can then launch various attacks, such as phishing or financial fraud. Often you only realize that something is wrong when it is already too late.
With our solution, you can stop such takeover attempts at an early stage. With several layers of protection, you can:
- Block phishing attempts aimed at stealing credentials.
- Monitor accounts to detect early signs of a takeover by analyzing suspicious behavior and using algorithms to detect irregularities.
- Act quickly when an account has been compromised to prevent further damage.
Many types of threats
Stop email-based threats before they reach users.
Cyber criminals are becoming more and more creative in their attempts to trick normal users. Our solution protects you against a wide range of threats and is constantly being improved and expanded to ensure that no threat is overlooked.
Collaboration apps
Protect not only emails, but also the most vulnerable collaboration tools.
Protect the collaboration tools in your company that are increasingly being misused for attacks. Use the integrated functions of the Cyber security solution, which combines backup, next-generation anti-malware and Cyber protection management functionalities.