Technical and organizational measures (TOM)
Version: Februar 2026
These technical and organizational measures apply to Netstream AG and Netstream Cloud AG.
Subject of the document
Dieses Dokument fasst die technischen und organisatorischen Massnahmen im Sinne von Art. 8 Abs. 1 DSG zusammen. Es beschreibt die Massnahmen, mit denen die Verantwortlichen personenbezogene Daten schützen.
Die Massnahmen sind eingebettet in ein zertifiziertes Informationssicherheits-Managementsystem (ISMS) nach ISO/IEC 27001:2022 und orientieren sich an den Schutzzielen Vertraulichkeit, Integrität, Verfügbarkeit und Belastbarkeit.
1. confidentiality
1.1 Access control
Massnahmen, die verhindern, dass Unbefugte Zutritt zu Datenverarbeitungsanlagen erhalten.
- Automatisches Zugangskontrollsystem mit elektronischem Schliesssystem und individuellem Berechtigungsmanagement
- Biometrische Zugangssperren in Rechenzentren
- Videoüberwachung in sicherheitsrelevanten Bereichen
- Klingelanlage mit Kamera in Büroräumlichkeiten
- Restriktive Zugangsrichtlinien und Wachpersonal
- Schlüsselregelung mit dokumentiertem Schlüsselbuch
- Visitor escort exclusively by authorized employees
- Alarmsysteme an allen relevanten Eingängen
- Vertragliche Absicherung mit Dienstleistern inkl. Geheimhaltungsvereinbarungen
- Sorgfältige Auswahl des Reinigungspersonals und vertragliche Absicherung
- Homeoffice-Richtlinie mit definierten Sicherheitsanforderungen
1.2 Access control
Massnahmen, die verhindern, dass Datenverarbeitungssysteme von Unbefugten genutzt werden.
- Persönliche Authentifizierung mit Benutzername und Passwort nach anerkanntem Industriestandard
- Zentrale Passwortrichtlinie mit Komplexitätsanforderungen und regelmässigem Wechsel
- Zwei-Faktor-Authentifizierung (2FA) für alle unterstützten Systeme
- Zentraler Passwort-Manager für sichere Verwaltung aller Zugangsdaten
- Endpoint Detection and Response (EDR) auf allen verwalteten Endgeräten
- Einsatz von Firewalls und Netzwerksegmentierung
- Verschlüsseltes WLAN nach aktuellem Standard mit separatem Gastnetzwerk
- VPN-Pflicht für alle Fernzugriffe
- Vollverschlüsselung von mobilen Datenträgern und Notebooks
- Remote-Wipe-Fähigkeit für mobile Endgeräte bei Verlust oder Diebstahl
- Automatische Desktopsperre bei Inaktivität
- Automatische Kontosperrung nach fehlgeschlagenen Login-Versuchen
- Deaktivierung inaktiver Konten
- Separate Konten für administrative Aufgaben
1.3 Access control
Massnahmen, die gewährleisten, dass nur auf die Daten zugegriffen werden kann, für die eine Berechtigung besteht.
- Rollenbasierte Zugriffskontrolle mit dokumentiertem Berechtigungskonzept
- Minimale Rechtevergabe nach Need-to-use-Prinzip
- Protokollierung von Zugriffen auf Anwendungen, insbesondere bei Eingabe, Änderung und Löschung von Daten
- Regelmässige Überprüfung der Zugriffsberechtigungen
- Professionelle Vernichtung von Datenträgern und Akten
- Physische Löschung von Datenträgern vor deren Wiederverwendung
- Sichere Aufbewahrung von Datenträgern gemäss Clean Desk / Clear Desk Policy
- Geregelter Entzug von Zugangsrechten bei Austritt oder Rollenwechsel
1.4 Separation control
Massnahmen, die gewährleisten, dass zu unterschiedlichen Zwecken erhobene Daten getrennt verarbeitet werden.
- Strikte Trennung von Produktiv- und Testumgebungen
- Logische Mandantentrennung in allen relevanten Anwendungen
- Netzwerksegmentierung mit definierten Sicherheitszonen
- Differenziertes Berechtigungskonzept mit Festlegung von Datenbankrechten
1.5 Pseudonymisierung und Datenminimierung
- Grundsatz der Datenminimierung bei jeder Datenerhebung
- Anonymisierung/Pseudonymisierung personenbezogener Daten bei Weitergabe oder nach Ablauf der Aufbewahrungsfrist
- Datenmaskierung bei Testdaten; Ausnahmen werden im Exception Management dokumentiert
2. integrity
2.1 Transfer control
Massnahmen, die gewährleisten, dass Daten bei Übertragung oder Speicherung nicht unbefugt gelesen, kopiert, verändert oder entfernt werden.
- Verschlüsselte Datenübertragung nach aktuellen Industriestandards
- Verschlüsselung ruhender Daten nach anerkannten kryptografischen Standards
- VPN-Tunnel für Fernzugriffe auf interne Ressourcen
- Bereitstellung von Daten ausschliesslich über verschlüsselte Verbindungen
- Keine Übermittlung sensibler Daten per E-Mail; Nutzung sicherer File-Sharing-Plattformen
- Dokumentation der Datenempfänger sowie Aufbewahrungsfristen
- Lieferantenmanagement nach ISO 27001 mit regelmässiger Überprüfung
- Automatisiertes Monitoring der kryptografischen Konfigurationen
2.2 Eingabekontrolle
Massnahmen, die gewährleisten, dass nachträglich überprüft werden kann, ob und von wem Daten eingegeben, verändert oder entfernt worden sind.
- Protokollierung der Eingabe, Änderung und Löschung von Daten
- Nachvollziehbarkeit durch individuelle Benutzernamen
- Zentrale Logging-Infrastruktur mit manipulationssicherer Speicherung
- Definierte Mindestaufbewahrungsfristen für Logs
- Zugriff auf Logs ausschliesslich für autorisierte Personen
- Regelmässige Kontrolle und Analyse der Protokolle
3. availability and resilience
3.1 Availability control
Massnahmen, die gewährleisten, dass personenbezogene Daten gegen zufällige Zerstörung oder Verlust geschützt sind.
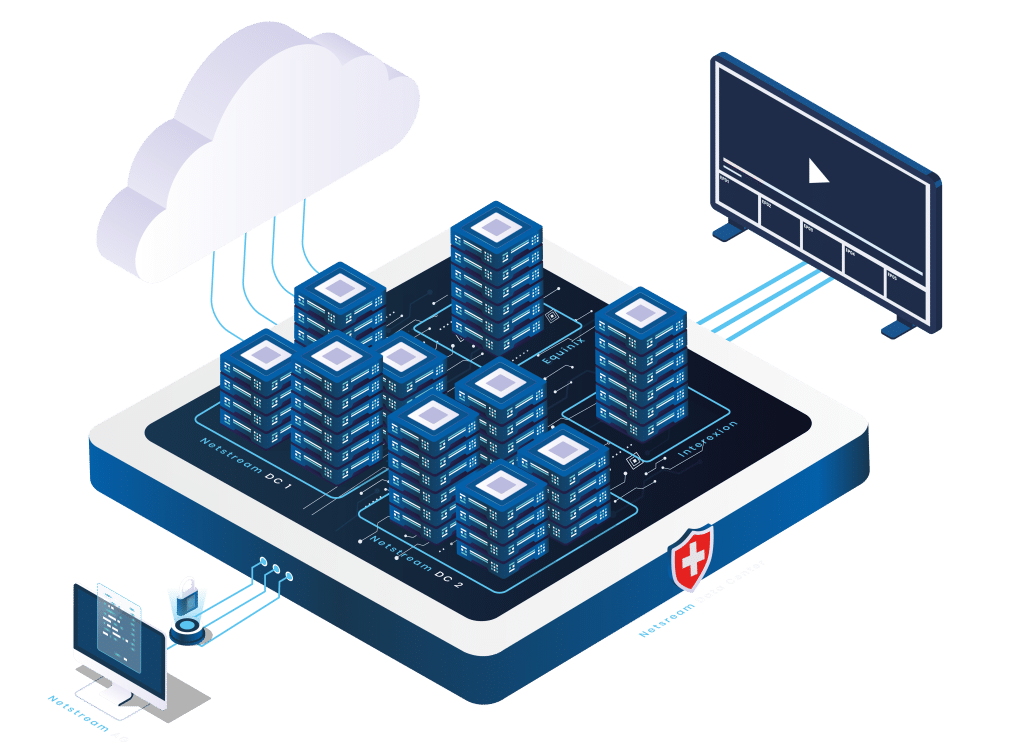
- Rechenzentren nach Tier-4-Standard mit vollständiger Redundanz
- Feuer- und Rauchmeldeanlagen sowie automatische Löschanlagen
- Klimaüberwachung in Serverräumen
- Unterbrechungsfreie Stromversorgung (USV) mit Notstromanlage
- Redundante Netzzuleitungen
- Redundanz-Architektur für alle geschäftskritischen Dienste
- Überwachung und Planung von Systemkapazitäten zur Vermeidung von Engpässen
- Regelmässige automatisierte Backups mit verschlüsselter Speicherung
- Aufbewahrung von Datensicherungen an sicherem, ausgelagertem Ort
- Dokumentiertes Backup- und Recovery-Konzept mit regelmässigen Tests
- Automatisierte Monitoring-Systeme mit Frühwarnung und Eskalationsprozessen
- Pikett-Organisation für zeitnahe Reaktion auf Systemstörungen
- Dokumentierter Notfallplan mit regelmässigen Tests
- Incident-Management-Prozess mit definierten Eskalationsstufen
4. Verfahren zur regelmässigen Überprüfung, Bewertung und Evaluierung
4.1 Informationssicherheit und Datenschutz
- Zertifiziertes ISMS nach ISO/IEC 27001:2022
- Interner Informationssicherheitsbeauftragter (CISO)
- Externer Datenschutzberater
- Verpflichtung aller Mitarbeitenden auf das Datengeheimnis
- Regelmässige Schulungen im Datenschutz und in der Informationssicherheit
- Regelmässige Sensibilisierungskampagnen inkl. simulierter Phishing-Tests
- Führen eines Verzeichnisses über Bearbeitungstätigkeiten (Art. 12 DSG)
- Systematisches Risikomanagement mit dokumentierter Risikoanalyse und -behandlung
- Klassifizierung aller Informationen nach definiertem Schema
- Richtlinie zur sicheren Nutzung von KI-Systemen
- Regelmässige interne und externe Audits
- Jährliche Managementbewertung mit Zieldefinition und KPI-Messung
- Einhaltung der Informationspflichten nach Art. 19 ff. DSG
4.2 Incident-Response-Management
- Dokumentiertes Incident-Management mit definierten Eskalationsstufen
- Meldeprozess für Datenschutzverletzungen gegenüber dem EDÖB (Art. 24 Abs. 1 DSG) und betroffenen Personen (Art. 24 Abs. 4 DSG)
- Einbindung des Datenschutzberaters bei Datenschutzvorfällen
- Endpoint Detection and Response (EDR) auf verwalteten Endgeräten
- Firewalls mit Netzwerksegmentierung
- Regelmässige Aktualisierung aller Systeme und Anwendungen
- Schwachstellenmanagement mit systematischer Erfassung, Bewertung und Behebung
- Sicherung von Beweismaterial in manipulationssicherer Umgebung
- Lessons Learned nach Sicherheitsvorfällen
4.3 Privacy-friendly default settings
- Schulung der Mitarbeitenden in Privacy by Design und Privacy by Default
- Datenerhebung auf das für den Zweck erforderliche Minimum beschränkt
- Anforderungen an sichere Softwareentwicklung und Codeüberprüfung
- Datenmaskierung und Anonymisierung bei Testdaten
4.4 Order control
- Schriftliche Weisungen an Auftragnehmer durch Auftragsverarbeitungsverträge
- Sorgfältige Auswahl von Auftragnehmern mit dokumentierter Bewertung
- Laufende Überprüfung und regelmässige Auditierung von Lieferanten
- Geheimhaltungsvereinbarungen für Lieferanten mit Zugang zu vertraulichen Informationen
- Sicherstellung der Datenvernichtung nach Beendigung des Auftrags
- Verpflichtung der Auftragnehmer auf das Datengeheimnis